Security and information at first hand
With its products, Beckhoff creates the technological foundation to ensure the cybersecurity of machines and systems. At the same time, we enable machine builders and equipment manufacturers to develop their own lean and efficient solutions. The key to this is providing detailed, transparent explanations and information about our technologies. We provide you with guidelines and practical application examples with background information ranging from methods to specific implementation.
Keeping watch on cyber risks
Actively monitoring and addressing cybersecurity vulnerabilities has been standard practice at Beckhoff for over a decade. We provide you with information about vulnerabilities in many ways:
- via the Beckhoff website at www.beckhoff.com/secinfo
- indirectly via national and international reporting offices such as the EU Vulnerability Database, the National Vulnerability Database in the USA, national offices in China, etc.
- via the CERT@VDE hub at https://certvde.com/en/advisories/vendor/beckhoff/
- and in a machine-readable form using the Common Security Advisory Framework (CSAF) format.
Good to know: Beckhoff publishes vulnerability reports in a machine-readable form using the CSAF (Common Security Advisory Framework) format. This allows companies to prepare as plant and machine builders should be able to efficiently monitor the vulnerability reports in future and evaluate them using their own bills of material (BOM, which also includes the software bill of material, SBOM). The CRA stipulates that in future they must be created and maintained for every system or machine that is assembled, delivered and installed. This will be almost impossible without semi-automated processing of vulnerability reports.
Beckhoff receives vulnerability reports via its Product Security Incident Response Team (PSIRT). It coordinates the handling and publication of vulnerability reports professionally using a process that has been established for over ten years.
Security guides on demand
We provide cybersecurity guides for all the products in the Beckhoff portfolio. You will find them at www.beckhoff.com/secguide. For over ten years, we have been providing background information, explaining the methods used and expanding our range of guides. In 2026, we will add examples of product scenarios in the EtherCAT fieldbus and provide their exemplary confirmation according to the IEC 62443 cybersecurity standard: as proof that Beckhoff products are ready for cybersecure use.
Certified according to ISO 27001
In 2026, Beckhoff Automation will be certified as a cybersecure supplier according to ISO 27001. We are also aiming to certify the development process for Beckhoff components in accordance with IEC 62443 part 4-1. For many years, we have been successfully applying the key elements required: these include threat modeling, design reviews, source code analyses, tests and component monitoring. The certification planned for 2026 will officially document the secure product life cycle.
Secure by design – with PC-based control from Beckhoff
The PC-based control technology from Beckhoff has enabled us to secure our control systems with the latest cybersecurity technologies from the range of standard operating systems for decades.
The Beckhoff guides demonstrates this (www.beckhoff.com/secguide) and explain how our products can be used as a gateway to separate the inner workings of a machine from its environment. The advantage? This allows the effort involved in implementing regulations, such as those required by the CRA, to be reduced significantly. This is because machine builders only need to establish ongoing vulnerability monitoring and rectification where there are actually points of attack.
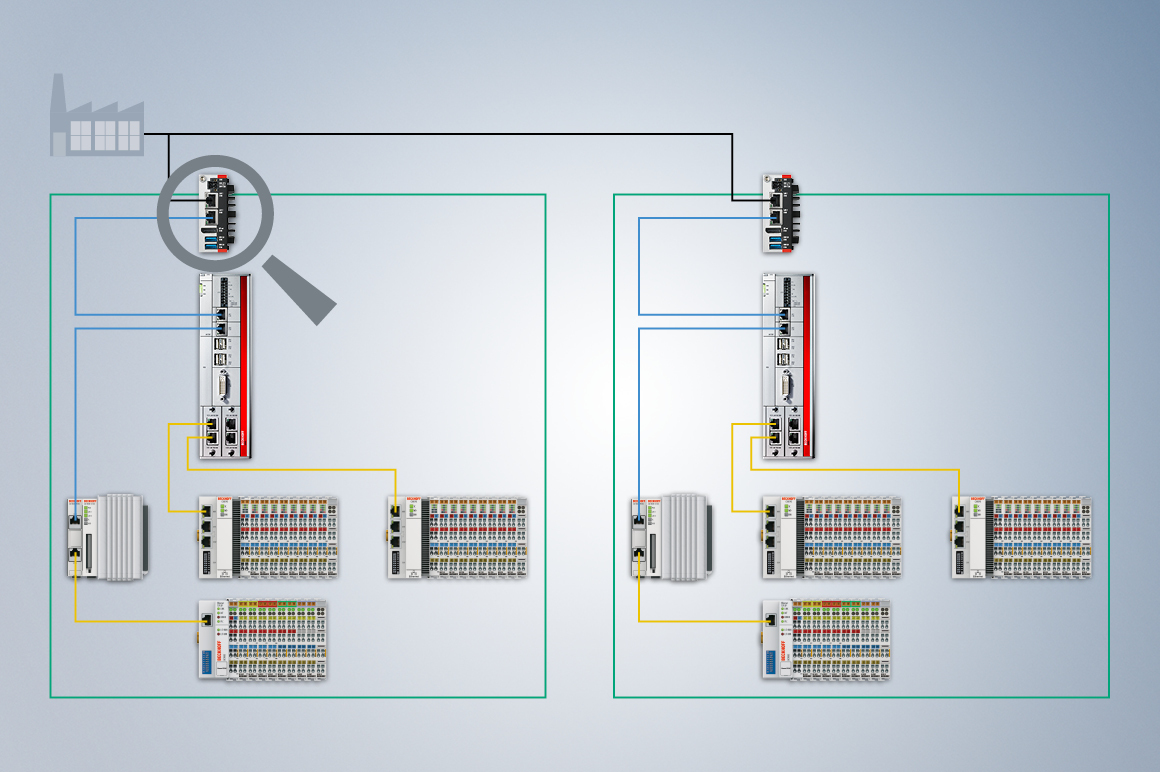
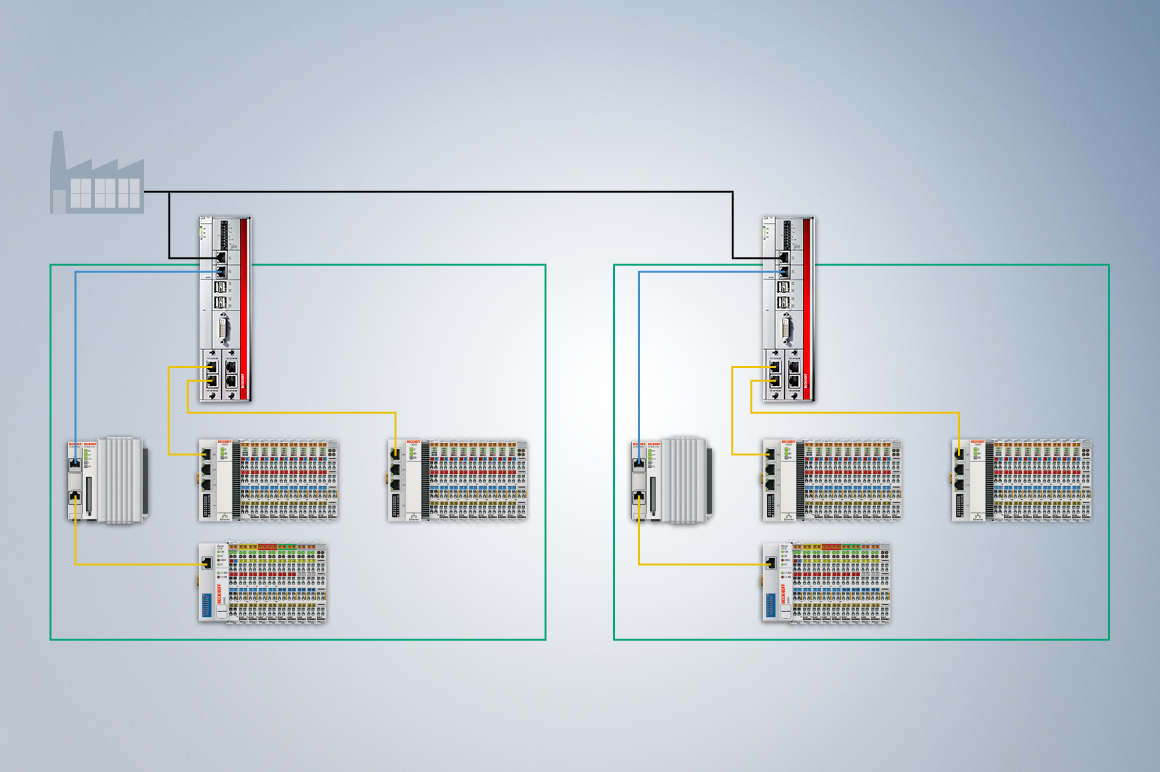
Example: A physical or virtual PC can act as a gateway for all communication with the environment or mediate between “inside” and “outside” in a controlled manner by means of a protocol break. While the inner PC is responsible for the real-time application, applications such as HMI, OPC UA Server and remote maintenance access can be implemented on the gateway via Secure Shell (SSH). Advantage: As a result, the system interior does not offer vulnerabilities and can remain as is. Only those applications that handle data communication with the system environment and the associated operating system require time-consuming vulnerability monitoring and rectification with updates.
Headquarters Germany
Beckhoff Automation GmbH & Co. KG
33415 Verl, Germany