Hannover Messe 2026
Beckhoff at the World’s Leading Trade Fair for the Manufacturing Industry


Program industrial robots via voice command
AI agent translates natural language into executable processes

Fast installation, commissioning, and maintenance
New EtherCAT Terminals enable tool-free installation and app-based diagnostics
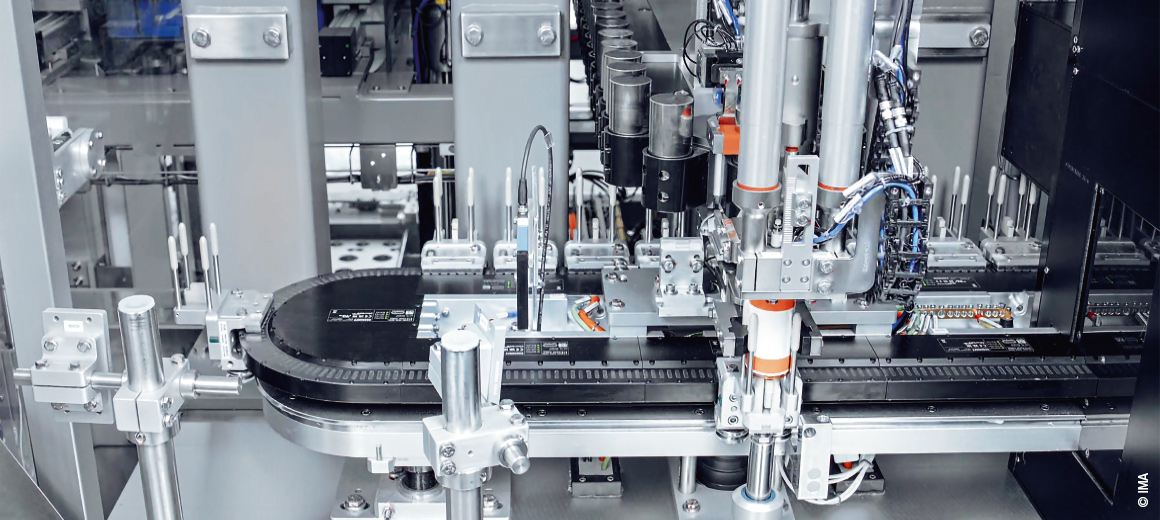
Efficient vehicle battery cell production
The XTS linear transport system reduces footprint while boosting productivity